 Table of Contents
Table of Contents
- What Is the HECVAT? The Complete Guide for Higher Education
- What Is the HECVAT?
- Why HECVAT Matters for Higher Education
- HECVAT Versions and Evolution
- What’s in the HECVAT Questionnaire
- How to Complete a HECVAT Assessment
- HECVAT Scoring and Results
- HECVAT 4: What Changed
- HECVAT vs Other Frameworks
- HECVAT vs Other Frameworks
- How to Simplify HECVAT Assessments
-
FAQ: Common HECVAT Questions
- What does HECVAT stand for?
- Who needs to complete the HECVAT?
- Is HECVAT free?
- What is the current version of HECVAT?
- What is the difference between HECVAT Full and HECVAT Lite?
- How often should HECVAT assessments be updated?
- Does HECVAT replace SOC 2?
- Is the HECVAT mandatory for higher education institutions?
- What if I prefer a custom questionnaire instead of the HECVAT?
- Where can I download the HECVAT?
- Key Takeaways
What Is the HECVAT? The Complete Guide for Higher Education
The Higher Education Community Vendor Assessment Toolkit (HECVAT) is a standard security questionnaire colleges and universities use to evaluate third-party technology vendors. Institutions send it to vendors during procurement, and vendors use it to disclose their cybersecurity, privacy, accessibility, and compliance practices. The institution then reviews those responses before approving the technology.
The current version is HECVAT 4.1.5, released February 10, 2025.
This guide covers what HECVAT is, how the questionnaire is structured, how institutions score vendor responses, what changed in HECVAT 4, how HECVAT compares with other frameworks, and how to simplify HECVAT implementation.
What Is the HECVAT?
The Higher Education Community Vendor Assessment Toolkit (HECVAT) is a free, standardized vendor security assessment built for higher education. It helps institutions identify risks before adopting new technology by evaluating how vendors protect sensitive data — including student records, research data, and institutional systems. Vendors describe their security controls, privacy practices, accessibility compliance, and operational safeguards.
The HECVAT (Higher Education Community Vendor Assessment Toolkit) is a standardized vendor security questionnaire higher education institutions use to evaluate third-party technology providers during procurement and vendor risk assessments.
The Higher Education Information Security Council (HEISC) developed HECVAT in partnership with EDUCAUSE, Internet2, and REN-ISAC. The toolkit launched in 2016 to replace the fragmented vendor assessment practices across higher education.
Today, hundreds of colleges and universities use HECVAT in their vendor risk management programs. K-12 institutions can use the K-12 Community Vendor Assessment Toolkit (K-12CVAT), created by CoSN (the Consortium for School Networking). K-12CVAT adapts HECVAT for primary and secondary schools.
Why HECVAT Matters for Higher Education
Before adopting new technology, institutions need to confirm that vendors can securely handle institutional data and meet regulatory requirements. HECVAT standardizes that evaluation.
Regulatory Compliance Requirements
Higher education institutions must comply with multiple data protection laws:
- FERPA (Family Educational Rights and Privacy Act) — governs student records
- GLBA (Gramm-Leach-Bliley Act) — applies to financial aid and student loan data
- HIPAA (Health Insurance Portability and Accountability Act) — applies to health-related data
- State data privacy laws and accessibility standards like Section 508 and WCAG add further requirements
As a result, every vendor that handles institutional data must be evaluated against these obligations. HECVAT helps institutions verify compliance.
Standardized Vendor Risk Evaluation
Before HECVAT, each institution created its own vendor security questionnaire. As a result, vendors received dozens of slightly different forms asking the same questions. The process was slow, inconsistent, and expensive for both sides.
HECVAT was built for higher education’s specific challenges: decentralized IT procurement, sensitive student data, and overlapping regulatory requirements.
Institutions now use HECVAT to run structured vendor risk evaluations during technology procurement. Cybersecurity, IT, privacy, accessibility, procurement, and legal teams review vendor responses using the same questionnaire and scoring framework. Vendors — cloud platforms, SaaS providers, and technology partners — describe their security controls, data protection practices, and compliance posture in the workbook. Institutions use the responses to identify risks, compare vendors, and support procurement decisions.
How HECVAT Improves Vendor Assessments
HECVAT improves vendor risk management in five areas:
- Standardized responses. Vendors complete one questionnaire and share it with multiple institutions.
- Consistent comparisons. Institutions evaluate comparable security and privacy data across their vendor ecosystem.
- Less duplicated effort. Vendors avoid completing multiple custom questionnaires.
- Faster procurement. Security teams evaluate vendor risk more efficiently.
How the HECVAT Assessment Process Has Changed
| Process Area | Previous Approach | HECVAT Approach | Outcome |
| Vendor questionnaires | Each institution creates its own questionnaire | Standardized HECVAT questionnaire used across institutions | Consistent vendor evaluation |
| Vendor responses | Vendors complete many similar questionnaires | Vendors complete one HECVAT assessment and reuse it | Reduced duplicated effort |
| Vendor comparison | Inconsistent formats across responses | Structured responses across vendors | Easier vendor comparison |
| Procurement reviews | Long review cycles and repeated questionnaires | Centralized questionnaire and scoring framework | Faster procurement decisions |
| Vendor risk programs | Difficult to scale across many vendors | Standardized assessments across ecosystems | Scalable third-party risk management |
In practice, these efficiencies reduce operational overhead significantly for institutions managing large vendor ecosystems through third-party security risk assessment programs.
HECVAT 4 expands the assessment scope with new AI and privacy questions, letting institutions evaluate risks from generative AI tools, machine learning platforms, and advanced analytics that vendors increasingly embed in their products.
HECVAT Versions and Evolution
HECVAT has evolved steadily since 2016. EDUCAUSE and the higher education security community have refined the toolkit through feedback from institutions, security teams, and vendors. Perhaps the biggest change came with HECVAT 4, which reorganized assessment structure and use.
HECVAT Timeline
| Year | Version | Key Changes |
| 2016 | HECVAT 1.0 | Higher Education Cloud Vendor Assessment Tool launched for evaluating cloud-based products |
| 2019 | HECVAT 2 | Renamed from “Cloud” to “Community.” Shifted from qualitative to Yes/No format with scoring. Added On-Premise and Triage versions. Expanded working group |
| 2020 | — | Became an official EDUCAUSE HEISC community group. Focus on adoption and usability |
| 2021 | HECVAT 3 | Revised questions, stronger accessibility focus, improved IAM content, reorganized sections, added NIST and ISO standards crosswalks |
| 2023 | HECVAT 3.05–3.06 | Streamlined documentation, added Trusted CI mappings for secure research |
| 2025 | HECVAT 4 (current: 4.1.5) | Single consolidated workbook replaces Full/Lite/On-Premise. New AI (32 Qs) and Privacy (69 Qs) sections. CBI retired July 2025 |
Earlier Versions (HECVAT 3 and Prior)
Earlier versions used separate questionnaires for different risk scenarios. Institutions chose the version matching the vendor’s risk level or deployment model.
HECVAT 3 included four questionnaires:
- HECVAT Full: 250+ questions across 22 sections. For mission-critical systems and vendors handling highly sensitive data.
- The Lite version included 62 questions covering 14 of 22 sections, designed for lower-risk vendors or rapid screening.
- An On-Premise version addressed software installed on institutional infrastructure rather than vendor-hosted.
- Finally, a Triage questionnaire served as a short pre-qualification screen to determine whether a full assessment was needed.
In practice, institutions and vendors often struggled to determine which version applied to a given product.
HECVAT 4: The Consolidated Toolkit
EDUCAUSE released HECVAT 4 on February 10, 2025. The current revision is HECVAT 4.1.5. HECVAT 4 combines the previous Full, Lite, and On-Premise assessments into one workbook.
Vendors answer a core set of questions, then complete additional sections based on their environment. As a result, this modular design eliminates version confusion and lets institutions scale the evaluation to match vendor risk and capabilities.
The High Risk Evaluation view aggregates critical and high-importance questions into a focused review — similar to the old HECVAT Lite — for evaluating lower-risk vendors efficiently.
EDUCAUSE provides migration documentation and change logs for institutions transitioning from HECVAT 3.
What’s in the HECVAT Questionnaire
The HECVAT 4 questionnaire contains 321 questions across seven sections. Each section covers a different layer of vendor risk — from organizational governance to product and infrastructure security, to specialized areas like AI and privacy. This structure lets institutions evaluate organizational security maturity and product-level controls in a single assessment.
| Section | Questions | Coverage |
| Organization | 43 | Company structure, security governance, policies |
| Product | 42 | Identity, authentication, logging, data security, operational safeguards |
| Infrastructure | 52 | Technical and operational hosting environment |
| IT Accessibility | 19 | WCAG 2.1 AA, assistive technology, accessibility documentation |
| Case-Specific | 64 | Consulting access, regulatory compliance, on-premises deployment |
| Artificial Intelligence (New) | 32 | AI development, deployment, governance, data privacy in model training |
| Privacy (New) | 69 | Personal and institutional data management throughout service lifecycle |
New Sections in HECVAT 4
HECVAT 4 added two sections reflecting emerging technology and regulatory concerns.
Artificial Intelligence
32 questions examine how vendors develop, deploy, and govern AI features — covering model training practices, data governance, and responsible AI oversight.
Privacy
The Privacy section includes 69 questions, making it the largest in the questionnaire. It evaluates how vendors collect, process, store, and dispose of institutional and personal data throughout the service lifecycle.
Question Types
HECVAT uses multiple formats to evaluate vendor practices:
- Binary: Yes/No/NA responses confirm whether a control or policy exists.
- Descriptive: Vendor explains how a control operates in their environment.
- Documentation: Vendors attach policies, audit reports, or certifications as evidence.
- Conditional (trigger): Certain answers activate additional sections based on the vendor’s deployment model or architecture.
As a result, institutions can verify both that controls exist and how they work.
Built-in Evaluation Tabs
The HECVAT workbook includes four evaluation tools:
- Institution Evaluation: Security teams record notes, scores, and review decisions.
- High Risk Evaluation: Aggregates critical and high-importance questions for focused review.
- Privacy Analyst Evaluation: Lets privacy teams assess data protection responses separately.
- Analyst Reference: Built-in guidance explaining each question’s intent to support reviewers.
How to Complete a HECVAT Assessment
The process starts when a department wants to adopt new technology — a learning platform, research tool, SaaS application, or other digital service.
Before approving the technology, procurement and security teams check whether the vendor will access or handle institutional data such as:
- Student records and PII protected under FERPA
- Research data from faculty or labs
- Financial or payment data protected under GLBA or PCI-DSS
- Protected health information under HIPAA
- Personal data governed by state privacy regulations
If the vendor handles sensitive data, a HECVAT assessment is part of the institution’s third-party risk review.
The HECVAT Assessment Workflow
Once a HECVAT review is required, the assessment follows six steps.
Step 1: Vendor receives the workbook. The vendor starts with the “Start Here” tab, entering basic information about the organization and product. Qualifying questions determine which sections apply.
Step 2: Conditional routing. Based on qualifying responses, the workbook directs vendors to relevant sections and marks the rest as not applicable. The Organization section is required for all vendors. A consulting firm with no product may only complete the Organization, Privacy, and Case-Specific sections.
Step 3: Vendor completes applicable sections. The vendor answers all relevant sections and provides supporting documentation — SOC 2 reports, security policies, or compliance certifications. In most cases, completion takes three to six weeks.
Step 4: Institutional review. Security or privacy teams review responses using the evaluation tabs. Reviewers mark responses as compliant or non-compliant, adjust importance levels, exclude irrelevant categories, and flag non-negotiable controls.
Step 5: Risk determination. An analyst interprets results in context — determining whether the vendor’s security posture aligns with institutional policies, regulatory obligations, and risk appetite. The institution decides whether to approve the vendor or require remediation.
Step 6: Ongoing monitoring. Schedule periodic re-assessments based on risk level. Monitor vendor updates such as new certifications, policy changes, or security incidents between cycles.
Best Practices
Vendors and institutions can improve HECVAT review efficiency with these practices.
| Role | Best Practice | Purpose |
| Vendor | Maintain current security documentation | Ensure policies, audit reports, and certifications are available for review |
| Provide clear, complete responses | Help reviewers understand how security controls are implemented | |
| Respond quickly to clarification requests | Reduce delays during the institutional review process | |
| Institution | Prioritize high-risk questions | Focus review on controls protecting sensitive institutional data |
| Define non-negotiable security requirements | Identify controls that must be in place before vendor approval | |
| Align reviews with risk policies | Ensure assessments reflect regulatory and institutional obligations |
Community Broker Index (CBI) Discontinued
Earlier versions included the Community Broker Index (CBI), a repository where vendors uploaded completed assessments for institutions to review. Over time, many stored assessments became outdated, reducing the repository’s reliability. Because the CBI was retired on July 31, 2025, institutions and vendors now exchange HECVAT assessments directly during procurement.
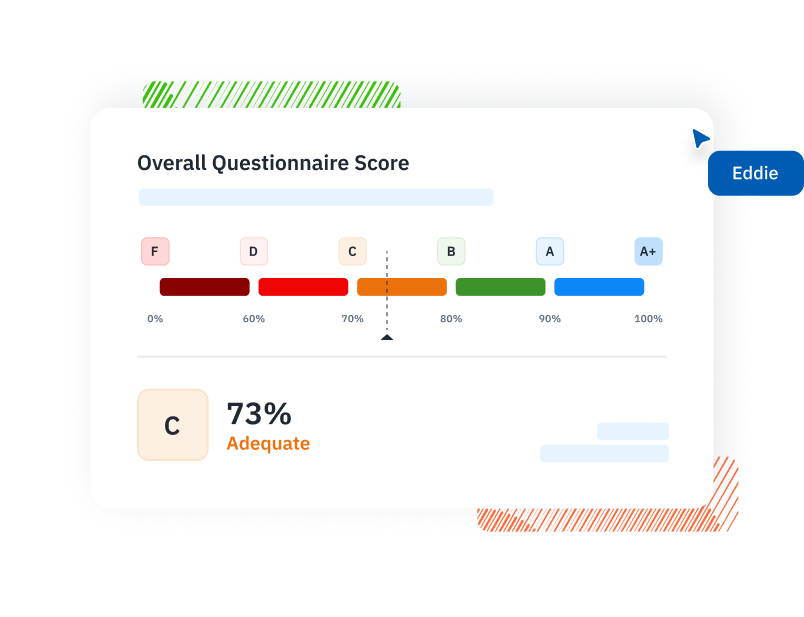
HECVAT Scoring and Results
HECVAT includes a built-in scoring model developed by higher education security professionals and vendors. The methodology reflects real operational and regulatory priorities.
Specifically, scoring takes place in the Institution Evaluation tab, where institutions review vendor responses, assign scores, and flag areas for further review.
How Scoring Works
Each question has a predefined importance level that determines how much it affects the overall score:
| Importance | Meaning | Score Impact |
| Critical | Controls considered essential for vendor risk evaluation | Highest impact |
| Standard | Core assessment questions | Moderate impact |
| Minor | Lower-priority questions | Lowest impact |
Each question also has a predefined compliant response.
- When the vendor’s answer matches, the question contributes positively to the score.
- When the answer differs, the score drops.
Institutional Customization
Institutions can adjust the scoring model to match their policies and risk tolerance:
- Override importance levels to reflect internal priorities
- Mark controls as non-negotiable — must be satisfied regardless of score
- Exclude irrelevant categories based on the vendor’s service
- Override compliant response defaults where institutional standards differ
Interpreting HECVAT Results
HECVAT provides three built-in views for interpreting vendor responses:
| Evaluation View | Purpose | How to Use |
| Institution Evaluation | Displays score summaries across security domains | Primary scoring and review workspace where analysts evaluate responses and record notes |
| High Risk Evaluation | Aggregates critical and non-negotiable controls for focused review | Used to quickly review the most important controls and identify major risk gaps |
| Privacy Analyst Evaluation | Allows privacy specialists to review data protection responses separately | Allows privacy or data protection teams to review data handling and regulatory compliance |
The HECVAT score is a decision-support tool, not a pass/fail grade. It gives institutions a structured basis for evaluating vendor security and making informed procurement decisions. Analysts start with a high-level review, then drill into domain-level scores. In turn, low-scoring categories prompt deeper examination of individual questions and vendor documentation.
How to Interpret HECVAT Results
Follow these six steps to move from raw scores to actionable procurement decisions.
Step 1: Review the overall score. Start with the aggregate score in the Institution Evaluation tab. A high score signals strong alignment with expected controls, but treat it as a starting point — not a final verdict.
Step 2: Break down results by category. Review domain-level scores across data handling, authentication, infrastructure, and incident response. Identify strong areas and gaps. A low infrastructure score, for example, may require follow-up on the vendor’s hosting environment.
Step 3: Compare vendors. Use HECVAT’s standardized format to benchmark vendors against each other. Category-level comparisons reveal which vendor best aligns with institutional requirements.
Analyze Gaps and Plan Remediation
Step 4: Review critical questions with unfavorable responses. Next, focus on critical-importance controls — they have the highest score impact and the greatest effect on institutional risk. If a vendor fails a critical control, determine whether the gap is fixable or disqualifying.
Step 5: Develop a mitigation plan. For each unfavorable critical response, document a remediation path. Work with the vendor on safeguards — improved access controls, encryption, vulnerability scans — and assign ownership and timelines.
Step 6: Document exceptions and schedule follow-up. Not every gap resolves before procurement. For accepted risks, document the exception, the rationale, and the conditions for revisiting the decision. Include exceptions in the vendor’s ongoing monitoring schedule.
HECVAT 4: What Changed
HECVAT 4, released February 10, 2025 (current version: 4.1.5), is the largest update since the toolkit launched in 2016.
- Consolidated format. Merges Full, Lite, and On-Premise into one assessment. Vendors answer core questions and complete additional sections based on their solution type. Redundant questions are eliminated.
- AI questions. 32 new questions cover how vendors develop, deploy, and govern AI features — including data privacy in model training, output transparency, and responsible AI practices.
- Expanded privacy assessment. 69 privacy questions, developed by the higher education Chief Privacy Officers community, cover personal and institutional data management. A dedicated Privacy Analyst Evaluation view lets privacy teams review responses separately.
- Stronger accessibility evaluation. Updated accessibility coverage addresses WCAG 2.1 AA compliance, documentation, and processes for reporting and resolving issues.
For details, see 2025 HECVAT Updates: What’s New in HECVAT 4.
HECVAT vs Other Frameworks
HECVAT vs Other Frameworks
HECVAT is built specifically for higher education technology procurement. Its questions address sector-specific concerns — FERPA student privacy, GLBA financial data, IT accessibility under WCAG 2.1 AA — that generic vendor risk tools do not cover.
The toolkit’s 321 questions align with NIST 800-53, HIPAA, and PCI DSS. Institutions already compliant with these standards can reuse existing control evidence when reviewing HECVAT responses.
| Framework | Focus | Purpose | Built-In Evaluation | Higher Ed Relevance |
| HECVAT | Security, privacy, accessibility, operations | Higher education vendor assessment | Yes — workbook with scoring and evaluation views | Highest — native to sector |
| CAIQ | Cloud security controls | Cloud service provider assessment | No — disclosure questionnaire analyzed externally | Medium — cloud-focused only |
| SIG | Broad enterprise third-party risk | Multi-industry vendor risk management | No — disclosure questionnaire analyzed externally | Medium — not sector-specific |
| SOC 2 Type II | Internal controls audit | Independent third-party audit | N/A — auditor report, not questionnaire | High — many vendors provide alongside HECVAT |
Detailed Comparisons
HECVAT vs. CAIQ: The Cloud Security Alliance’s CAIQ contains 261 questions focused on cloud security controls. HECVAT’s 321 questions cover a broader scope — security, privacy, accessibility, AI governance, and operations — with built-in evaluation workflows. CAIQ is primarily a disclosure questionnaire analyzed externally.
HECVAT vs. SIG: The SIG questionnaire supports enterprise third-party risk programs across industries. HECVAT targets higher education specifically and integrates evaluation tools directly into the workbook. SIG responses are analyzed through separate processes.
HECVAT and SOC 2: SOC 2 reports support the HECVAT review but do not replace it. SOC 2 may cover privacy if the Trust Services Criteria for Privacy is in scope, but HECVAT evaluates additional domains — accessibility and AI governance — that SOC 2 does not address. Most institutions use HECVAT as the primary assessment and reference SOC 2 as supporting evidence.
When to Use Each Framework
Use HECVAT when a vendor processes institutional data or integrates with campus systems. CAIQ applies to cloud infrastructure evaluations. SIG fits enterprise third-party risk programs at large organizations.
How to Simplify HECVAT Assessments
Running HECVAT assessments across dozens or hundreds of vendors gets difficult fast. Tracking which vendors have been assessed, which questionnaires are outstanding, and which results need review is where institutions hit a wall. However, spreadsheets, shared drives, and email threads do not scale when vendors move through different assessment stages simultaneously.
Isora GRC is the collaborative GRC Assessment Platform™ built for security teams. With a purpose-built HECVAT Uploader, vendors submit responses directly into the platform while reviewers manage everything in one shared workspace.
- Centralized assessment visibility. See every vendor assessment’s status from one dashboard — send questionnaires, collect responses, and track documentation in one place.
- Connected vendor inventory. Maintain a single inventory of vendors, products, and services linked to HECVAT assessments. Always know which vendors have been evaluated and which reviews are outstanding.
- Collaborative review workflows. Security and privacy teams review responses together, record findings, and track follow-up actions — no email chains or shared spreadsheets.
- Risk tracking and audit-ready reporting. Link results to a risk register, prioritize remediation, and generate audit-ready reports for procurement decisions and compliance documentation.
HECVAT 4’s expanded scope — 321 questions across seven sections, new AI and privacy domains, dedicated evaluation views — increases assessment complexity. Isora GRC helps institutions adopt these changes with confidence.
Streamline your security GRC workflows with Isora GRC
FAQ: Common HECVAT Questions
What does HECVAT stand for?
Higher Education Community Vendor Assessment Toolkit. HEISC, EDUCAUSE, Internet2, and REN-ISAC developed it to help institutions evaluate third-party vendor security, privacy, accessibility, and compliance practices.
Who needs to complete the HECVAT?
Vendors working with higher education institutions. You typically complete the HECVAT during procurement or contract renewal. The institution’s security or compliance team reviews your responses as part of its vendor risk assessment.
Is HECVAT free?
Yes. EDUCAUSE holds the copyright but makes the toolkit available at no cost. Institutions can modify the questionnaire for internal use. Software vendors that want to embed HECVAT in commercial products need an EDUCAUSE license.
What is the current version of HECVAT?
HECVAT 4 (revision 4.1.5), released February 10, 2025. It consolidates the previously separate Full, Lite, and On-Premise questionnaires into a single workbook.
What is the difference between HECVAT Full and HECVAT Lite?
In HECVAT 3 and earlier, Full (250+ questions, 22 categories) and Lite (62 questions, 14 categories) were separate questionnaires. HECVAT 4 merges them into one assessment. The High Risk Evaluation view aggregates the most important questions for focused review, serving the same purpose as the old Lite.
How often should HECVAT assessments be updated?
Most institutions reassess based on vendor risk tier: annually for high-risk vendors (mission-critical, sensitive data), every two years for medium-risk, and every two to three years for low-risk. Vendor incidents, acquisitions, or material security changes may trigger immediate reassessment.
Does HECVAT replace SOC 2?
No. HECVAT is a self-assessment questionnaire. SOC 2 Type II is an independent third-party audit. SOC 2 reports support the HECVAT review but do not replace it. Most institutions require both — HECVAT as the primary assessment, SOC 2 as supporting evidence.
Is the HECVAT mandatory for higher education institutions?
No. HECVAT is not legally required but is highly recommended. It helps institutions build a vendor risk management program that supports compliance with GLBA, HIPAA, CMMC, and NSPM-33. Many institutions adopt HECVAT to standardize evaluations, reduce duplicated effort, and build repeatable assessment processes.
What if I prefer a custom questionnaire instead of the HECVAT?
A well-completed HECVAT often works better than a custom form. Vendors already know the questions, responses are comparable across institutions, and the built-in scoring model provides immediate evaluation structure. Custom questionnaires can supplement HECVAT for institution-specific needs, but replacing it entirely reintroduces the fragmentation HECVAT was designed to solve.
Where can I download the HECVAT?
From the EDUCAUSE website (free account required). The current file is HECVAT 4.1.5.
Key Takeaways
HECVAT is the standard vendor assessment toolkit for higher education, used by hundreds of colleges and universities to evaluate third-party technology providers.
HECVAT 4.1.5 consolidates earlier questionnaire formats into a single modular workbook. Vendors complete one questionnaire with sections that apply to their service — no more choosing between Full, Lite, or On-Premise. New sections cover AI governance and expanded privacy evaluation, and accessibility requirements are strengthened.
To run an assessment, send the workbook to the vendor during procurement or contract renewal. Vendors typically take three to six weeks to complete the questionnaire and provide supporting documentation. Review responses using the built-in scoring views and determine whether the vendor meets institutional risk requirements or needs remediation.
Ultimately, understanding the questionnaire structure, scoring model, and alignment with NIST 800-53, HIPAA, and PCI DSS is essential for effective vendor risk management in higher education.
See how Isora GRC simplifies HECVAT assessments →
This content is for informational purposes only and does not constitute legal or compliance advice. See our full disclaimer.


















